Mobile proxy.
What does it mean?
What is a "mobile IP-address"?
Due to the specifics of the mobile Internet, the mobile IP address is unique in its parameters as a technical solution. Since the mobile operator has a huge number of subscribers who use Internet services, it is technically impossible to give each subscriber a static IP address, but most importantly, it is not profitable for the mobile operator itself.
It is much more convenient to create a single pool of IP addresses, and assign it to several subscribers at the same time. From this it follows that hundreds or even thousands of mobile Internet subscribers can work simultaneously on a single mobile IP address. Because of this, large Internet resources and social networks require adjustments in their ban systems and access restriction algorithms. If a large resource, such as Facebook, blocks one of the mobile IP addresses, then thousands of users may be blocked.
What is a "mobile proxy"?
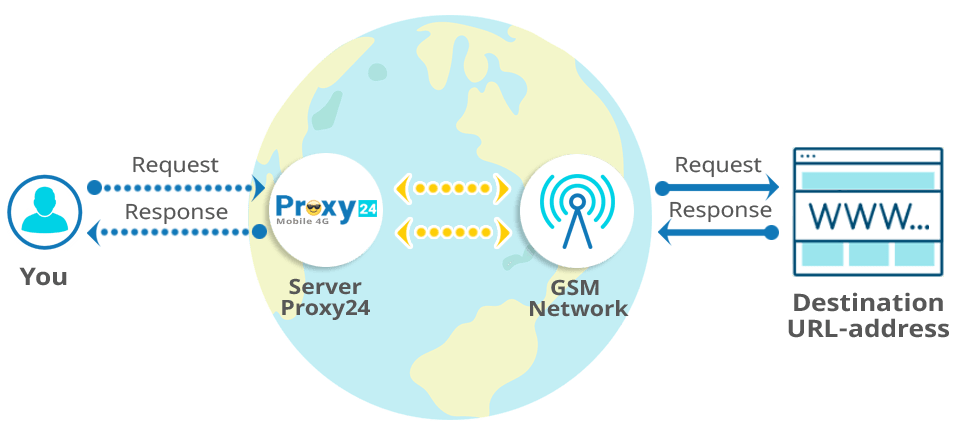
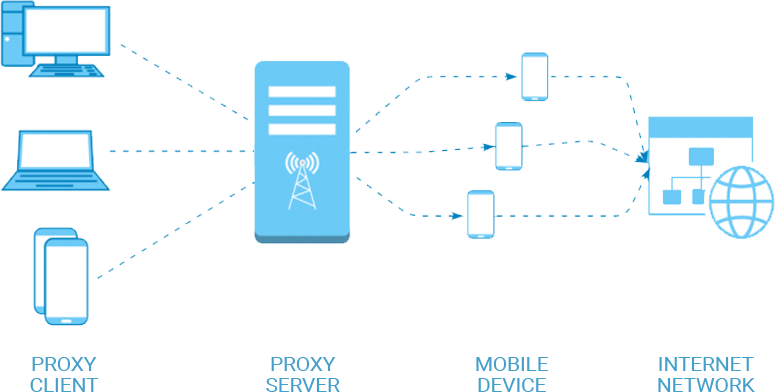
Mobile proxies are a software and hardware complex that serves as an intermediary between the Internet and the user. Mobile proxies provide data exchange by proxying the user's web requests via the mobile Internet from the GSM operator.
In this format of work, all user requests on the Internet will pass through the mobile operator using a mobile IP address. This will allow to use the Internet and get all the advantages of working in the mobile network of the GSM operator.
How do mobile proxies work?
There are quite a few approaches to implementing mobile proxy. Many services and companies use different approaches to create mobile proxies. The most high-performance and reliable is the redirection of traffic from real SIM cards to internal servers.
In this format, the absolute advantage is the use of real mobile devices when working with a SIM card and the network of the mobile operator as a whole. The mobile device is completely valid authentication in the network of the mobile operator, with the entry of IMEI in the register of the cellular node. After that, the proxy server begins to control data transfer through these mobile devices, allowing you to pass any requests through the mobile Internet in the GSM-operator network.
Mobile proxy servers allow you to create a high-quality access control system, can limit the bandwidth on a separate channel, create dynamic pools of mobile IP-addresses and implement the work of mobile proxies on different protocols (SOCKS5, HTTPS).
What is the difference between mobile proxies and classic proxies?
Ordinary proxies, as a rule, use IP addresses of hosting providers or cloud services, which by definition cannot belong to an individual. So, this activity simply can not be a real user. Such an IP in 90% of cases becomes the cause of blocking at the slightest suspicion of “suspicious activity” from the point of view of ban systems and algorithms of large Internet resources.
Алгоритмы выявляют используемый адрес и применяет конкретные действия: блокирует или понижает уровень траста к аккаунту.
How does mobile IP blocking work? The mobile operator assigns addresses from its own pool to users with a limited number of IPv4 addresses. It turns out that several million users share only a couple of hundred IPs, which are distributed among all devices using NAT.
Therefore, if the algorithm blocks the IP address of the cellular operator, then this action is reflected on ordinary users working under the same IP. And the loss of the target audience is extremely undesirable for social networks or large portals.